After reading about the “suicide” of yet another whistleblower, it got me thinking.
When working at large enough company, it’s entirely possible that at some point you will get across some information the company does not want to be made public, but your ethics mandate you blow the whistle. So, I was wondering if I were in that position how I would approach creating a dead man’s switch in order to protect myself.
From wikipedia:
A dead man’s switch is a switch that is designed to be activated or deactivated if the human operator becomes incapacitated, such as through death, loss of consciousness, or being bodily removed from control. Originally applied to switches on a vehicle or machine, it has since come to be used to describe other intangible uses, as in computer software.
In this context, a dead man’s switch would trigger the release of information. Some additional requirements could include:
- No single point of failure. (aka a usb can be stolen, your family can be killed, etc)
- Make the existence of the switch public. (aka make sure people know of your mutually assured destruction)
- Secrets should be safe until you die, disappear, or otherwise choose to make them public.
Anyway, how would you go about it?
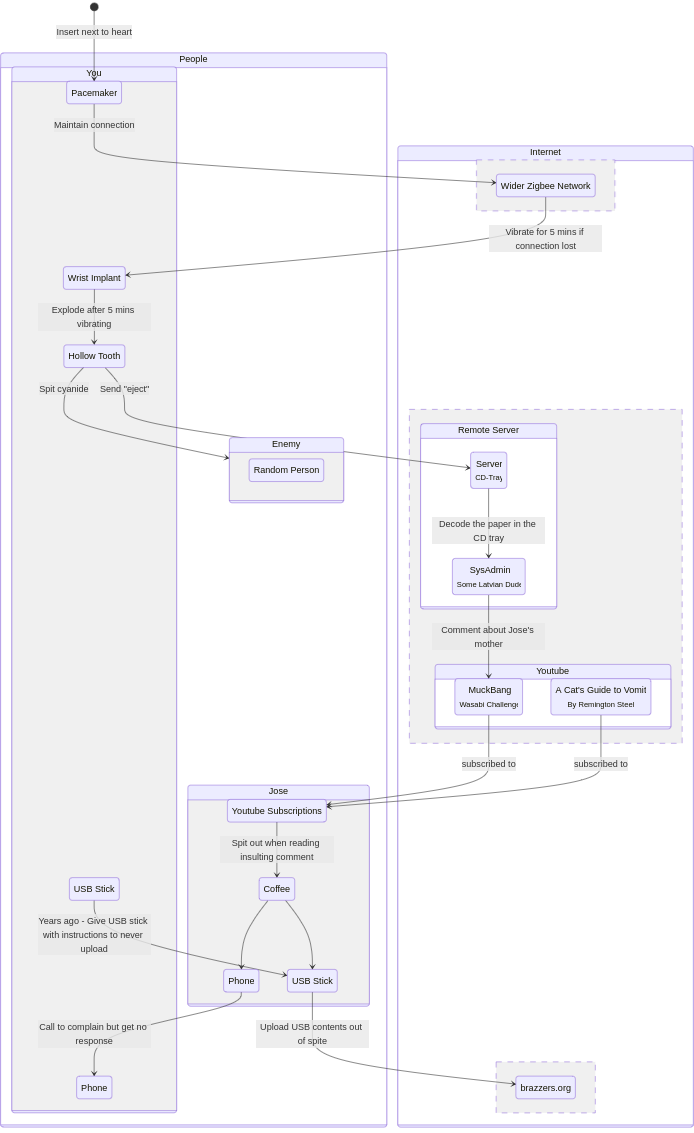
The most non-intrusive foolproof method I can think of is spite-induced action:
- Get a pacemaker with Zigbee mesh network connectivity
- Implant a small device into your wrist that vibrates if your pacemaker is ever disconnected from the network (in which case, run NOW to your nearest safehouse)
- Should the vibration continue for longer than 5 minutes, a vial of cyanide from a hollow tooth explodes into your mouth allowing you to spit it at your nearest enemy (should one be around)
- The bursting of the hollow tooth sends a signal to a remote server, which triggers the
ejectcommand on a server, causing the CD tray to come out. - A confused sysadmin will bitterly get off his chair, and go inspect the server, whereupon he will see the paper instructions embedded in the CD tray, and read them.
- Assuming his latvian is good, and that he’s familiar with caesar cyphers, he will decode the message that will lead him to a youtube URL where he will post the following comment “Jose I slept with your mother.”
- One of the subscribers to the youtube channel is your friend Jose, who will read the comment, spit out his coffee, and then immediately call you.
- After about a week of no response, he uploads the contents of that USB stick you gave him with the instructions to “never upload this ever under any circumstance” out of sheer spite.
Edit: Here, I made a diagram of the whole thing
State Diagram
(with mermaid source)
stateDiagram-v2 direction TB state Internet { state "Wider Zigbee Network" as WiderZigbeeNetwork -- state "Youtube" as youtube{ state "MuckBang <small>Wasabi Challenge</small>" as video1 state "A Cat's Guide to Vomit <small>By Remington Steel</small>" as video2 } state "Remote Server" as server { state "Server <small>CD-Tray</small>" as cdtray state "SysAdmin <small>Some Latvian Dude</small>" as terry } -- state "brazzers.org" as brazzers } state People { state "Jose" as jose { state "Youtube Subscriptions" as subs state "Phone" as josephone state "Coffee" as cuppajoe state "USB Stick" as usb2 } state "You" as you { state "Pacemaker" as pmaker state "Wrist Implant" as wrimplant state "Hollow Tooth" as htooth state "USB Stick" as usb1 state "Phone" as youphone } state "Enemy" as enemy { state "Random Person" as rando } } [*] --> pmaker : Insert next to heart pmaker --> WiderZigbeeNetwork : Maintain connection WiderZigbeeNetwork --> wrimplant : Vibrate for 5 mins if connection lost wrimplant --> htooth: Explode after 5 mins vibrating htooth --> cdtray: Send "eject" htooth --> enemy: Spit cyanide cdtray --> terry : Decode the paper in the CD tray terry --> video1 : Comment about Jose's mother video1 --> subs : subscribed to video2 --> subs : subscribed to subs --> cuppajoe : Spit out when reading insulting comment cuppajoe --> usb2 cuppajoe --> josephone usb1 --> usb2 : Years ago - Give USB stick with instructions to never upload josephone --> youphone : Call to complain but get no response usb2 --> brazzers : Upload USB contents out of spiteThis reads like a modern day SysAdmin Rube Goldberg machine; I love it
Worthy of being submitted to The Register as a sysadmin story
LEMMY GOLD ahahahaha
Woa, I was reading this as the Edit federated in and it refreshed. Trippy.
I love it!
Wallfacer Diaz?..
Eh?
Oh, just a silly reference to the sifi series “Rememberance of Earth’s Past” by Lui CiXin. A character, Manuel Rey Diaz, makes a convoluted dead man’s switch device in order to attempt to defend against an impending alien invasion. Incredible series, highly recommend 😁
Oh! Ive read that trilogy, I love that standoff he has when it looks like he’s about to kill himself. Didn’t make the connection
The real answer: hire a law firm, entrust them with your documents, write into your will what you want to happen with them, and then go on about your business.
Maybe, add a clause what should happen if you disappear for more than x days. For most jurisdictions you are considered dead if you disappear for a few years.
The question assumes that you family could be killed. Why the law firm is protected against such violence in that case?
A dead man’s switch doesn’t quite protect you from garden hose cryptanalysis though. Nothing stops them from asking you to tell them if he got a dead man’s switch.
This is only partially true in the situation the poster named. What if your secrets are from the government or governmental organization? What if you live under a repressive regime where the law firms are either corrupt or that the law is not in your favor?
That being said, I have a will and a bank safe deposit box. It is filed with the state that I have a will and the will is (also) in the safe deposit box along with stuff that I’d prefer not be released until my death. There’s also a clause in the will that says something to the effect that if somebody sues to invalidate the will, they are automatically excluded from any benefit (or responsibilities). Also, if an individual is found to be somehow responsible or had an intentional involvement in my death, then they are also excluded.
It’s not air tight, but works for my needs. By the way, I don’t have any company or government secrets, it’s just normal family drama, so please don’t kill me.
Only correct answer here.
Encrypt secret. Post it publicly. Configure a web server to email the private key to any number of addresses if you don’t log in every week.
going to have to be careful with the timing, though. A week can easily be reached if you are ever in an (actual) accident.
Also, note that having a publicly known dead mans switch can be exploited and cause the opposite of what you want: Imagine a competitor (be it idustrial or nation state) wants the secret to leak. Why not speed it up?
The thought of e.g. some foreign adversary having you KILLED just so your secret leaks… that’s wild.
Host the server on Tor. Have a second secret server on Tor that passively monitors the health of the first and distributes the key if it is taken down. Have a one-time pad of passwords memorised, not written down or taken from a book.
Ciphers get broken. What you save out there now can be pulled down and then saved until it can be cracked 10 years from now.
On that subject makes me wonder if insurance.aes has been cracked yet
That’s an optimization for just having the automated email send the secret directly.
depending on the size of the secret, it helps to have people download it ahead of time.
Also, it acts as a time stamp proving that you knew the secret at a certain time if that’s useful.
Right, that’s what i mean by optimization. It’s accomplishing the same goal, but amortizes the transfer over more time, saving bandwidth.
The timestamp feature could also be accomplished by publicly posting a small hash of the data ahead of time, but similarly bandwidth can be optimized by distributing the encrypted blob ahead of time.
There are very few situations where a dead man’s switch would have helped these whistleblowers.
Once they have gone public and are at risk of being “suicided” they should have already released everything they knew. Sitting on it after already going public in any way only helps if the goal is to blackmail or extort the company, rather than to expose the company or protect others.
A lot of people have latched onto the idea of a dead man’s switch (and I get it, technical solutions are fun to create), but the only part of the scenario it would help is before the whistleblower goes public, while they are still gathering information and haven’t yet been discovered by the company. Even then, it wouldn’t protect them from being killed, it would only ensure that the partial work is released in case they were discovered and prevented from finishing it.
A “live-man’s switch” might be a better idea. If you’re in such a high profile situation and you’re scared enough that you think you need a dead man’s switch, make frequent unprompted public declarations that you’re healthy and not suicidal, and that should anything happen to you, you blame the company.
Btw, that sounds a lot like warrant canaries, where you say that no subpoena orders were recieved as of the date xxxx and if it doesn’t get updated it means that a subpoena was recieved.
Wikipedia article: https://en.m.wikipedia.org/wiki/Warrant_canary
An example of a canary from the web mail service cock.li: https://cock.li/canary.asc.txt
Interesting!
make frequent unprompted public declarations that you’re healthy and not suicidal
I’ve worried that this could be abused
Didn’t help McAfee
If you really have secrets, you shouldn’t have a dead man’s switch.
You should have released it all on day one.
“What makes them keep you alive then?”
It’s not like corporations are going to get punished for killing you regardless.
The problem with releasing them on day one is that you then can’t gather more. If you’ve only just exposed the edges of the malfeasance you need time to get the rest before exposing it. Go too early and the rest of the evidence can be destroyed, covered up or those holding it coearsed into silence.
Having a dead man’s switch is a way to ensure whatever you’ve gathered gets released if you’re no longer in a position to gather more. As such I disagree with the poster about making it public knowledge before release. Keep it secret until you have everything, then release it.
Another thing to consider is that you won’t know immediately that the information you stumbles upon is incriminating. Sometimes it may take years until you have all the pieces of the puzzle.
Fwiw I’ve actually thought about a dead man’s switch for a while now. When my partner and I were going through end-of-life stuff, having the ability to delete or open things as needed after you’re dead can be important.
I have a rough design in my head where you register various monitors (e.g. checking email, logging into Lemmy, etc) and so long as you reach a specified threshold you’re considered alive.
Build in a duress code or dead code that can be entered by your next of kin, then you got something workable.
For a dead drop like you described in your OP, I agree that instructions to an attorney is probably your best bet. But in the scenario you’re describing, it sounds like having this code won’t be valuable.
Just a scheduled email that you need to cancel every 24 hours.
That more like coalmine canary than dead man switch. Also, if you happen to be arrested on a weekend or get tangled/hooked up then you will have no way of cancelling it. Then all hell breaks loose.
Could set it up like every month. It’s what I would do anyway, simple enough to set up. Low chance of anyone being able to do anything about it
Make it 60-72 hours and your death will still be fresh enough for it to be relevant, but plenty of time to figure out how to work around whatever calamity might prevent still-alive you from stopping it. It’s even enough time that if your death makes the news it’ll have been seen by most relevant journalists and newsrooms already so they’ll have more context for the strange email they find
The fuck kind of information you sitting on there!?
He knows the real identity of the Hamburgler
The McDonald’s CEO? He’s a criminal after all
Nothing atm, but you never know what you may find. I would assume that most whistleblowers didn’t know they joined a shady organisation until years down the line…
This one works if you are an inbox-zero sort of person. Write a script to send yourself an email daily. Have another utility look for your reply. If you go too long without replying, have it trigger whatever other emails/actions you would like to happen.
they can just smash the computer with the scripts running
Anyone with less capabilities of a medium sized nation-state will not be able to “just smash” an AWS datacenter.
that’s right, they can just ask amazon to shut it down
How will they even know it exists until the switch is triggered?
4, 8, 15, 16, 23, 42
Making the existence of the switch public is often something you don’t want. It allows others to do troubleshooting in advance. It also destroys your reputation with many people who might otherwise work with you.
If you are content to keep things secret, share the documents with several different friends or law firms in several different countries along with conditions for release. Don’t tell them or everyone who all has the documents. That sounds relatively simple.
Making the existence of something public means you’d need to give away at least some details of who or what it concerned, at which point you’re in the situation of either being a target or a blackmailer.
I agree with all of the above, except I’d add encryption to the data.
That way you are not putting your life in their hands, at least until it doesn’t matter / you want the data released. Encryption keys are super lightweight vs data; taken to an unreasonable extreme, a KB could unlock TBs.
Though you’d probably want something more like a passphrase. Anyway, that basic idea is sound but I dunno about the exact delivery/delay mechanism. Gun to my head and I have seconds to decide… scheduled send from a major cloud email provider, pay way in advance, and an increasing flood of calendar events/reminders up to the day it sends. The message would include enough information about the encryption used and formats within that any tier 1 helpdesk level IT person could access the data.
Not perfect, but a good enough balance of simple and robust to start with.
Give the encrypted file to one person, the key to another and do not keep either yourself. They exchange them if you die.
Why not keep a copy?
Also, both people are single point of failures. Maybe, 5-6 people where each has an encrypted payload and the keys to decrypt everyone else’s payload.
IIRC Julian Assange had something like that set up. There used to be a file you could download from WikiLeaks that was encrypted and supposedly contained something very spicy, and if anything happened to him the password would be released somehow.
No idea if that’s still a thing or not though.
Nice try Boeing.
My lips are sealed
Pretty easy if you don’t work for google.
- Upload everything to a google drive.
- setup inactive account manager
- add all the news agencies you can get a hold of, government offices, police etc.
- make sure it’s read only access.
If they want to silence you they have to 1. Know about your account. 2. Keep it active.
It relies on the news agencies and such actually caring.
As someone who’s been fighting a huge fight against a casino threatening my performance home, lemme tell you that most don’t give a single shit
Everything relies on someone caring, in this context.
The whole point in being a whistleblower is to release the documents. Why would you tell everyone what’s happening and not provide the evidence? After you release it, there’s less chance of being harmed, and your job is done besides showing up to court.
Maybe he wants to release a censored version of the documents and have the dead man switch release the uncensored version.
Depends on your background and industry.
If you work in IT, and are technically adept, you can…
- Store said files on a proton drive or mega.nz drive set to be only accessible to read by those who have the unique URL.
- Create a small server with a cron job that every 24 hours sends you a text message to a Google Voice number accessible anywhere with internet connectivity and you have 60 seconds to reply otherwise the cron job will craft a premade email to all international news agencies as well as government agencies responsible for the control of this issue, along with links to download the information.
60 seconds in 24 hours seems too prone to the possibility of a false positive. What if you forget and take a nap? What if there’s a power outage? What if your phone breaks unexpectedly?
All good points, however the purpose of a deadman’s switch is that you fear for your life, taking a nap might not be as easy under those circumstances. Also, if you know at what time the SMS is set to arrive you can plan ahead to make sure you have Internet in order to respond, but OK maybe 60 seconds is too short of a time so let’s make it 5 minutes. Being that this is using Google Voice, you can receive the SMS over a tablet or laptop so a backup would be a must have.
Even 5 minutes seems short. You’re already dead, what’s the rush?
You don’t want to give the people chasing you time to identify and disable the deadmans switch
That’s why you create a backup deadman’s switch.